Can your Hosting Service Get Hacked?

If you’re a website owner, you know that the data on your site can be stolen or destroyed by hackers. However, it may surprise you to learn that hosting companies are also subject to hacking risks. The good news is that you can take steps to minimize the chance of this happening. Here’s what you need to know:
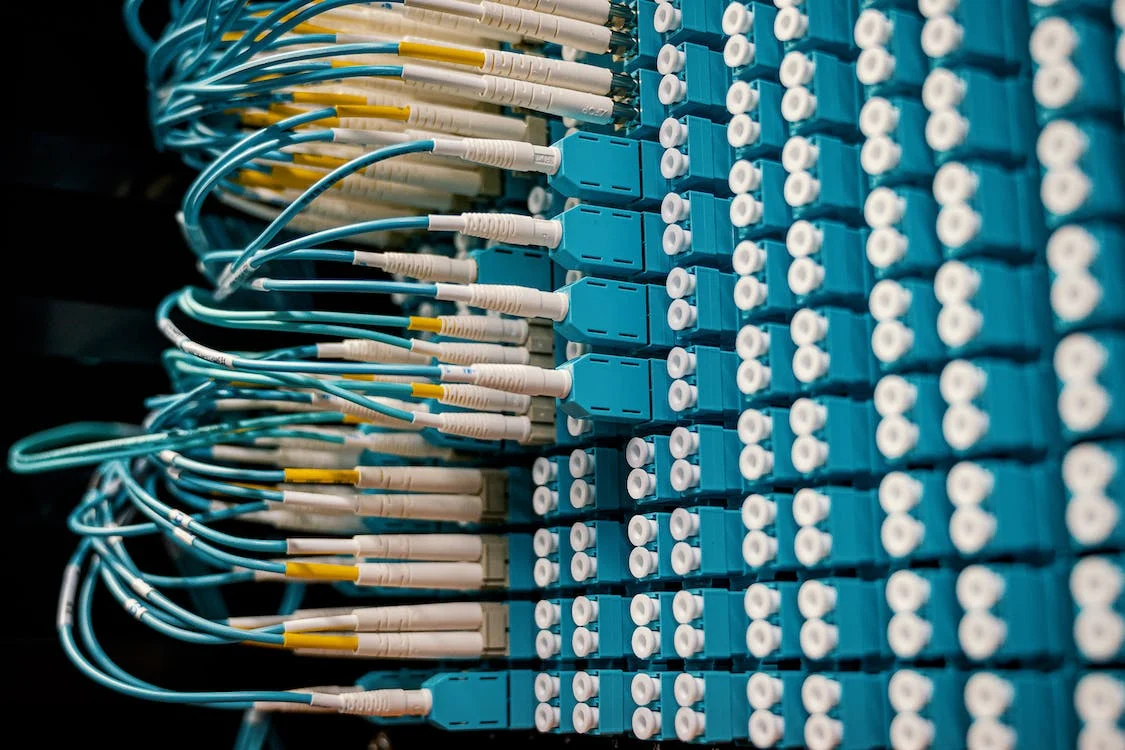
Hosting Companies Take the Data of Many Websites and Store It on Their Servers
The data is stored in a server room, server farm, or even a server cluster. Server rooms are full of several racks of each type of computer that the company uses to power its hosting service. Servers themselves are not put into these racks directly; instead, you’ll find what’s called “hard drives” inside those racks. Essentially, these hard drives are storage devices for all your files and data!
A hard drive contains an immense amount of memory that allows it to store information like text documents, photographs, and videos — basically anything you can think of!
If a Hosting Company Gets Hacked, the Hacker May Gain Access to All the Sites That Are Hosted On That Server
A hacker might try to compromise one site or all of them. In this case, you’d have to worry about your site getting hacked but also about other sites being compromised as well.
In some cases, hackers can use this kind of attack to steal credit card information from people who purchase products and services from the affected websites. Also, you should be aware of the warning signs of your cybersecurity failing.
The Risks Are High, and You Should Use Caution When Selecting a Hosting Service
Many companies will offer to host your website for free or a nominal fee, but it’s important to ensure that the company is reputable. Do your research on the company before signing up with them—check out their reviews, look at the number of customers they have, and find out if there have been any complaints filed against them by past clients. If you’re not sure whether or not you can trust the hosting service that you’re considering, it’s better to pass on them altogether until you have more information.
Following are some ways to ensure you are choosing a safe and secure web hosting provider:
1. Ask your Hosting Service If They Have a Firewall to Protect Against Hackers
Many web hosting services offer a firewall. A firewall is a piece of software or hardware that monitors your website for attacks and blocks malicious activity, such as hacking attempts.
A common type of firewall is called a software-based firewall, which uses rules to dictate what traffic can and can’t pass through it. For example, if you have a rule that allows traffic from the IP address range 10.0.*.* but not from other ranges (like 192.*.*), the software will block all traffic except what comes from within that range (which may include legitimate sites). Another type of firewall is hardware-based; these use real network devices like routers or firewalls to filter out unwanted traffic before it reaches your site’s server.
You should ask your host if they offer a security feature like this before choosing them as your host provider; if they don’t offer one and you’re concerned about being hacked, look elsewhere.
2. Make Sure Their Encryption Technology is of the Highest Standards Possible
You should also ensure that your host’s encryption technology is of the highest standards possible.
They should be able to provide documentation of their encryption technology, as well as information on how it protects your site from hackers. In addition, make sure they keep backups of their data at all times and can quickly restore your website if things go wrong.
3. Secured Data Centers
Data centers are the physical location of your web hosting server. They are often referred to as “data centers” or “colo.” A colocation center that specializes in housing servers is called a data center, which can be thought of as a building dedicated to housing servers and other network hardware.
Data centers are generally located in secure areas with restricted access and monitored by security cameras, sometimes around the clock. The facilities generally have regular temperature control systems that keep them cool, dry, and dust-free—which helps ensure optimal conditions for your server’s hardware. Most data centers also have redundant power supplies and backup generators in case of an outage or power disruption, so you can rest assured that all your files will remain safe even if an emergency situation affects your area.
In general, it’s best to choose a hosting provider that has its own dedicated data center rather than relying on third-party providers like DigitalOcean because this gives you more control over how things work behind the scenes (such as making sure they use strong encryption for all transfers).
4. File Permissions
File permissions are a measure of how accessible a file is to other users. They’re divided into three categories: read, write and execute. Each category can be set to one of three levels: read (read-only access), write (write-only access) or execute (executable by the user).
If you ever see a message that says, “The owner has denied this request,” it’s likely because someone else has changed your file permissions. In this case, try changing them back (using chmod) to their normal settings before attempting again.
5. Malware and Spam Scanning
As the owner of the site, you can also take a precautionary step by having your hosting service scan for malware and spam and improve your cybersecurity. This can be done in two ways: through your hosting company and with third-party software.
Hosting companies typically offer anti-malware scanning as part of their standard package, so you may not need to do anything beyond paying for it. If you do choose to use third-party software, make sure it’s compatible with your host before installing it on their servers (and don’t forget to uninstall all unnecessary add-ons).
Spam filtering services are typically user-configurable from within an email client such as Outlook or Gmail; just look under “filters” or “rules.”
6. Access to Core Files
Giving access to your core files is a bad idea. The server should be configured to deny access to these files, and if you’re a developer, you should be able to change them. However, if someone has access to your server and can change its configuration, they could create an exploit that would allow them access again.
If you are a developer and need file editing capability on your site (for example, installing WordPress plugins or changing PHP settings), we recommend using SSH tunneling software like PuTTy or Terminal on Mac OS X as an alternative method of accessing the remote server instead of FTP/SFTP clients, such as Filezilla.
7. Good Customer Support
Good customer support is important. The best hosting service providers know this, and they make it clear to their customers by providing excellent customer support.
When you sign up for a hosting plan, you should expect the company to be able to help you with any issues that come up. A good hosting provider will be able to quickly resolve any problems that arise and explain things clearly so that you understand what’s happening and why.
It’s also nice if your host offers live chat or telephone support as well as email ticketing—that way, if one method doesn’t work out for some reason, there are other options available as back-ups in case something goes wrong when using technical solutions (like forums).
How to Prevent Your Hosting Account from Being Hacked?

1. Keep Your Password Strong
The most common way people get hacked is through weak passwords, which can be easily guessed or cracked by brute force attacks. This isn’t just a problem with your hosting account; it’s also a problem with other accounts you use online (like email, Facebook, and Twitter).
To prevent this from happening to you, use a password manager like LastPass or 1Password to generate and store unique passwords for every account you have.
2. Enable Two-Factor Authentication for Any Service That Offers It (Including Your Hosting Provider)
Two-factor authentication (2FA) adds an extra layer of security by requiring something you know (your password) in addition to something you have (your phone). Some services will send one-time use codes via text message when you log in from a new device; others will generate these codes themselves after having verified the login attempt against their own systems—with either method being sufficient protection against most hacks that involve guessing passwords.
If a hacker doesn’t have access to your phone number or email address as well as knowing what your password is, they won’t be able to log into any of the sites where two-factor authentication was enabled successfully without first breaking into both accounts individually first.
3. Don’t Forget to Update Immediately
Make sure all software updates are installed immediately. This is especially important for WordPress software updates because they often fix vulnerabilities that have been discovered in previous versions of the software.
In addition to that, you should always stay up to date with all the trends in cyber security so you don’t ever have to worry about getting hacked.
4. Read Customer Reviews
These days, most hosting companies have their own websites with testimonials from happy customers. If they don’t, try searching for reviews on third-party sites such as Google My Business or Yelp.
It’s also important that you read through negative and positive reviews. This way, if there are any consistent issues being reported by customers (such as poor support), then you’ll know whether or not it’s something worth considering before signing up with them.
A Good Hosting Provider Will Do Everything in Its Power to Minimize the Risk of Getting Hacked
If you are hosting a website, there are several things that your host can do to minimize the risk of a hack. They should have firewalls in place to protect against hackers and encryption technology to protect data. They should also keep multiple backups of your data at all times and have excellent customer support and security practices.
Just make sure to use 2FA and a strong password, so you don’t have to deal with hackers on your side.